Structural reshaping of the international order upon the end of the Cold War caused a redefinition of the Russian Federation’s political position in the new constellation of power and, in a long-term perspective, initiated a revision of the state approach to the Russian foreign policy concept. Feeling of historic humiliation with the events from the end of 20th century, feeling of endangerment caused by the NATO enlargement on the East, together with the exclusion from the post-Cold War European security architecture, incited Russian authorities to opt for the open confrontation with the (pro)Western countries, rather than the peaceful coexistence.
Such an approach to the foreign policy requested defining the new hybrid operation strategy (war) where the borders between the levels of war became blurred. However, its actors remained the same – Russian intelligence services.
The intelligence system of the Russian Federation, mostly inherited from the former state system and burdened by the complex organizational reforms, managed to consolidate and grew into the strong system, which, together with the Russian Orthodox Church, media and organizations would become one of the major pillars of the modern Russian foreign policy.
For years, Russia did not hesitate to use intelligence agencies as an important foreign policy and hybrid operation tool, while affirming the subversive actions as a means to reach its geopolitical goals. Therefore, the intelligence services of the Russian Federation undoubtedly have an important role to renew Russian global influence and strengthen the Russian state. The political appointments of the former members of the intelligence-security system confirm these claims.
Since the annexation of Crimea in 2014, the subject of Russian intelligence services whose operations are directed abroad, became global. In this context, two institutions stand out – Foreign Intelligence Service and Military Intelligence Service.
Foreign Intelligence Service or SVR (Служба внeшней разведки – СВР) was founded in 1991 by President Yeltsin’s decree, as one of the Soviet KGB’s successors. The legal foundation of the SVR is the Constitution of the Russian Federation, federal and other acts that regulate the work of the federal services. The goals of the intelligence operations of this and other services are stipulated by the Federal Law on Foreign Intelligence (Федеральный закон “О внешней разведке”) from 1995. According to the Law, the SVR collects and processes the intelligence information on the Russian Federation’s vital interests being threatened (by the states, organizations, and individuals). The main domains of the service are: political, economic, military-strategic, scientific-technological, and ecological, while the greatest part of the resources is used for foreign policy intelligence work. The Service also represents the evaluative and political force that contributes to the creation of the Russian foreign policy. Its headquarters is in Moscow while its residencies are located in the Russian diplomatic-consular and commerce offices all around the world.
Military Intelligence Service or GRU (Гла́вное разве́дывательное управле́ние – ГРУ, or Гла́вное управле́ние – ГУ) was founded in 1921 and represents a strong professional military intelligence organization that performs within the General Staff of the Armed Forces of the Russian Federation. Its legal foundation is also composed of the Constitution, Law on Foreign Intelligence, and other legal and strategic documents of the Russian Federation. The GRU is responsible for the collection of intelligence data referring to the foreign military potentials and military plans of the foreign countries directed towards the Russian Federation. Collecting intelligence data is performed by using electronic systems, observing and investigating the activities of the armed forces of the countries from the immediate environment, observation satellite systems, and applying human intelligence. Generally, the activities and tasks of this service may be classified into two elementary groups: counter-terrorist activities and espionage. Central and Eastern Europe are the main areas of GRU operations.
The Federal Security Service or FSB (Федеральная служба безопасности Российской Федерации – ФСБ), formerly (1994-1995) Federal Counterintelligence Service is a Russian service for the interior security and counterintelligence affairs, founded in 1994 as one of the KGB successors from the Soviet era. It is responsible for the counterintelligence services, anti-terrorism, and supervision of the Army. The FSB is located in the former KGB headquarters on the Lubyanka Square in Moscow. In 1998, Boris Yeltsin appointed Vladimir Putin for an FSB director, a former KGB veteran who later succeeded Yeltsin as Federal President. Yeltsin also ordered FSB to extend its operations against trade unions in Siberia and fight the right dissidents. As a president, Putin increased the authority of the FSB by including countering the foreign intelligence operations, fighting against organized crime, and suppressing the Chechen separatists in their scope of work. The FSB is the largest security service in Europe and is exceptionally successful in counter-intelligence activities. Even though particular limitations over the FSB activities within the country have been imposed (such as reduced spying on religious institutions and charitable organizations), the FSB as well as other Russian intelligence services is subject to a smaller control of legislation or judiciary.
Operations of the Services as a Foreign Policy Tool
The doctrine of the contemporary Russian activity is attributed to Valery Gerasimov, Chief of the General Staff of the Armed Forces of Russia, who published the article titled The value of science in prediction in February 2013. The article is considered the most useful articulation of the contemporary Russian strategy. It offers a new theory of modern warfare, representing a combination of the Soviet psychological tactics and strategic military thinking on total war, reminding more of the hostile countries’ hacking, rather than an open, frontal attack (usage of hackers, media instrumentalization, fake news creation, information leak, presence of the businessmen, together with the conventional and asymmetric military tools). The following is written in the article: The very ‘rules of war’ have changed. The role of nonmilitary means of achieving political and strategic goals has grown, and, in many cases, they have exceeded the power of force of weapons in their effectiveness. (…) All this is supplemented by military means of a concealed character.
In March 2016, Gerasimov stated that each government ministry, not just the Ministry of Defence, needs to be capable to support hybrid warfare, and that “falsification of events [and] restriction of activity of mass media… can be comparable to the results of large-scale use of troops and forces.
The application of Gerasimov’s doctrine can best be analyzed on the example of the European countries, with some of them being NATO member countries. In just a couple of months in 2021, it was more than obvious that Moscow did not sit idly. In that period, four GRU actions on the territory of Europe and NATO members (Bulgaria, Czech Republic, Italy, and Germany) were revealed. Russia has been performing actions against the USA and its partners and allies for years, through the services and organizations controlled by the Kremlin. The examples include military support to the separatist republics in the East of Ukraine, a coup attempt and cyber operations in Montenegro as well as the campaigns of influencing in the USA during the presidential election in 2016 and 2020. Electoral interference in France 2017, poisoning of a Russian-British double agent Sergei Skripal in Great Britain in 2018, the hacking attempt of the Organisation for the Prohibition of Chemical Weapons (OPCW) in Hague also in 2018, and many attempts of direct interference into electoral processes in other countries clearly indicate the reach of Russian foreign policy implemented through the secret services.
Response to such actions usually came down to the expulsion of Russian diplomats and imposing of economic sanctions, which additionally became meaningless with lack of continuity and cohesion between the Western countries and allies.
Annual reports of the State Department, the EU, and NGOs all around Europe indicate the wide spectrum of techniques that Russia is using to exert its political influence through its power leverages (including SVR and GRU), and offer particular details on the implementation of these activities that are believed to aim at changing European politics and decision making, and therefore – weakening of NATO and the EU.
For numerous mentioned reasons, the Western Balkans represents a fertile ground for the implementation of the Russian strategy, since it is very important due to its geographic position.
Services in the Field
For a long time, Russian intelligence services in the region have been engaged in the local propaganda offensives in the media, online and on social media, but also in the field, in order to strengthen the Russian prestige and influence but also to undermine the credibility of the state institutions. The operations performed in this forever-turbulent area have been conceived in order to attract Eurosceptic, anti-American, and ultraconservative social subjects and individuals, to whom Russia is presented as a defender of traditional values and Orthodoxy.
Moscow openly threatened to Montenegro and NATO alliance on several occasions. In December 2015, the Kremlin spokesman Dmitry Peskov threatened that Russia would know how to fight back if Montenegro joins NATO, and the Russian Parliament threatened to freeze all projects with Montenegro. Ignoring these Russian warnings, the then Prime Minister of Montenegro Milo Djukanovic signed in May 2016 the NATO accession protocol, permanently depriving Russia of the only potential ally with maritime access to the Mediterranean. In June 2016, spokeswoman of the Ministry of Foreign Affairs Maria Zakharova stated that the then-Montenegrin government would be completely accountable for the anti-Russian stance that it allegedly took.
The goal of the coup attempt was primarily to stop Montenegro’s accession to NATO but also to install the new government in Montenegro, the one that would be led by the pro-Russian Democratic Front. In May 2019, the High Court in Podgorica sentenced two Russian citizens Eduard Shishmakov and Vladimir Popov to 15 and 12 years in prison. The Democratic Front leaders Andrija Mandic and Milan Knezevic were sentenced to five years in prison respectively, while the former Serbian police general Bratislav Dikic was sentenced to eight years in prison. Predrag Bogicevic and Nemanja Ristic, members of the extreme right-wing organizations from Serbia, who were unavailable to the Montenegrin judiciary, were sentenced to 7 years of prison respectively. The driver of the Democratic Front Mihajlo Cadjenovic was sentenced to one year and six months in prison, Branka Milic, the citizen of Serbia who escaped to the Serbian Embassy in Podgorica before the very end of the trial was sentenced to three years in prison, Serbian citizen Milan Dusic was sentenced to one year and a half, Dragan Maksic to one year and nine months, Srboljub Djordjevic to one year and a half and Kristina Hristic got suspended sentence.
In February 2021, the Appellate Court of Montenegro abolished the first-instance verdict since, during the procedure, the violation of the criminal procedure provisions was made. . Retrial for attempted terrorism on the parliamentary Election Day in 2016 in Montenegro, which was supposed to start on May 31, was postponed for October 19 due to the strike of Montenegrin lawyers.
Eduard Shishmakov was traveling to Serbia with a Russian passport under the name of Eduard Shirokov. Under this name, Montenegro issued a red notice through Interpol on February 19, 2017. Montenegrin Special State Prosecutor Milivoje Katnic said that Shirokov’s real name was Shishmakov, which was revealed thanks to the tip from the Polish partner services
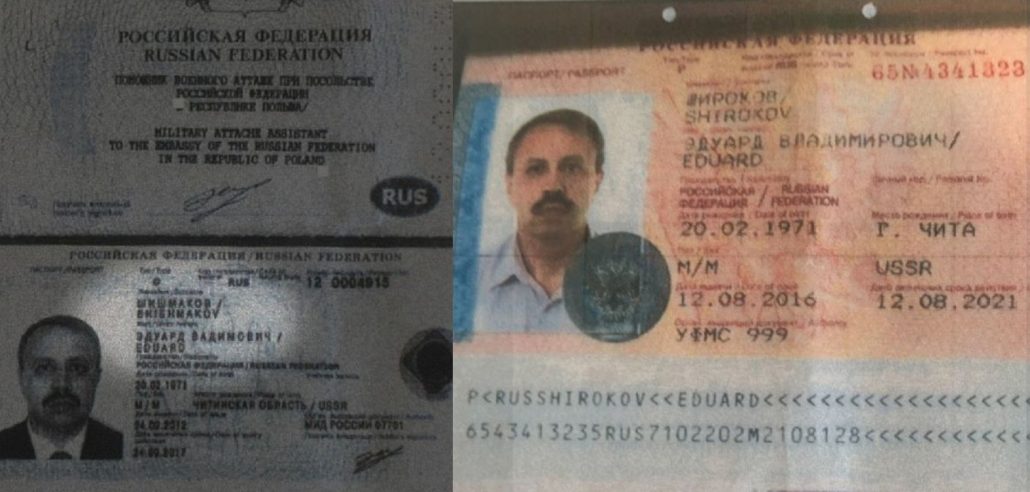
Since 2013, Shishmakov was a naval attaché in the Russian Embassy in Warsaw. As the most prominent investigative media Bellingcat reveals, Shishmakov took part in the high-level security meeting with the Polish Security Council on January 24, 2014. On the Russian part, the meeting was attended by Deputy Secretary of the Security Council Evgeny Lukyanov (Deputy of Nikolai Patrushev), as well as the Head of Center for Defense of the Russian Institute for Strategic Studies of the Kremlin, Grigory Tishchenko. In November 2014, Polish media reported that the Russian diplomat was declared persona non grata and expulsed. In March 2017, Polish authorities confirmed to Sky News that the diplomat was Eduard Shishmakov. His residential address is in Sankt Peterburg, and according to Bellingact, the address belongs to a corporate residential complex owned by GRU.

Vladimir Popov is another GRU agent who was sentenced to 12 years in prison upon the first instance verdict. Bellingcat and Insider managed to reveal the true identity of Popov – Vladimir Nikolaevich Moiseyev. Moiseyev, a lieutenant colonel or colonel (Belingcat could not claim for sure) in the Russian intelligence service, was born on June 29, 1980, the same day as the made-up Popov. Bellingcat states that in 2009, Moiseyev was given a new identity under the name of Vladimir Popov.
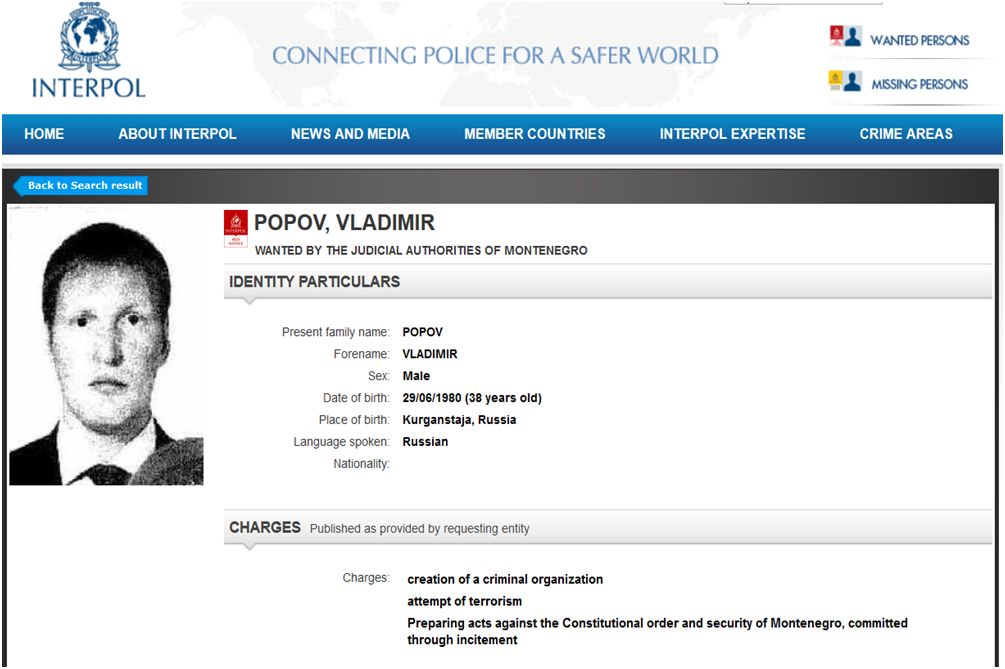
Just like his colleagues from the GRU Chepiga and Mishkin, who are suspected of poisoning a Russian-British double agent Sergei Skripal and his daughter in Great Britain with a nerve agent, Moiseev has two parallel identities in the Russian databases– Vladimir Moiseyev and Vladimir Popov. Also, in March 2015, Moiseyev was given an apartment in the same residential building where Mishkin obtained it a couple of months ago. Just like in the case of Mishkin, the apartment is registered in the name of Moiseyev’s wife and children while the GRU agent’s name was not stated in the document on the property. Popov was employed as a photo correspondent and journalist who worked for the magazine and used this identity to travel around Europe between 2012 and 2016. Claiming to be a Morskoye Strakhovanie journalist, Popov traveled to Serbia in October 2016. A couple of days before the parliamentary election in Montenegro, Popov, and Shishmakov met in Belgrade, which is visible in the surveillance camera footage.
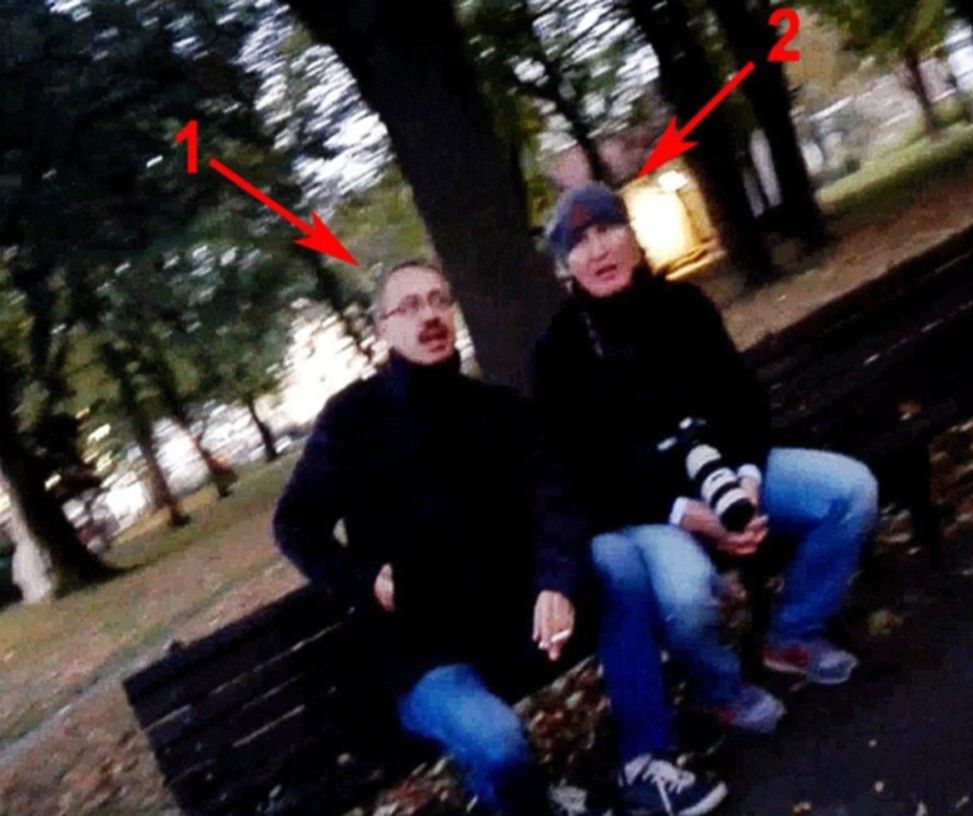
Secretary of the Security Council of the Russian Federation Nikolai Patrushev traveled to Belgrade on October 26, 2016, for the previously scheduled visit. At the beginning of November, the Guardian quoted a source close to the Serbian government who said that Patrushev had apologized to the Serbian authorities for, as he described, rogue operation. Russia later publicly denied these claims and characterized them as a provocation.
Patrushev has a significant role in the creation of Russian politics towards the Balkans. In the period until 2015, Moscow lacked a central authority figure that would significantly contribute to the implementation of the Russian goals in the Balkans. Patrushev, former Director of the Russian Federal Security Service, a close associate to Putin, known for his aggressive and strong stances, was a perfect person to assume that role. As a result, Putin appointed him the key person of the Kremlin for the Balkans at the end of 2015 or 2016 (depending on the source). Patrushev is accused of taking part in the organization of the coup d’état in Montenegro. Besides, he was ardently advocating for the construction of the Serbian-Russian Humanitarian Centre in Nis, considered a cover-up for military-intelligence operations in Serbia and the region. What particularly instigated claims that it is a Center that Russian intelligence services operate from, is the fact that the official Moscow, on several occasions, sought from Serbia to delegate special status to the Russian staff employed in the Center, through the Agreement on terms and conditions of the residence, privileges, and immunity of the staff. The first Russian intelligence officer, Director of the Foreign Intelligence Service, Sergey Naryshkin, said in an interview given to RTS that delegating diplomatic status to the Serbian-Russian Humanitarian Center in Nis was not a request but an appeal to Serbia and that it had not been done so far due to the pressure of particular Western countries.
Cyberspace
Russian activities in cyberspace represent an integral part of the comprehensive framework of hybrid warfare, derived from the Russian understanding of soft power and relations among countries, more precisely, the zero-sum game of the great powers for the influence in the world. Just like other aspects of the Russian soft power, the Kremlin perceives cyberspace in a geopolitical sense.
The Russian concept of information warfare and role of the cyberspace in it is exposed in the strategic policy documents such as the National Security Strategy (2015 and 2021), Foreign Policy Concept (2016), Doctrine of Information Security of the Russian Federation (2016), Military Doctrine of the Russian Federation (2014), as well as the works and publications of the Russian military strategists.
Interference in the U.S. presidential elections in 2016 is the most documented case demonstrating the Russian modus operandi. This interference included the attacks on the U.S. election infrastructure, collecting, and intentional data leaking of the Democratic Congressional Campaign Committee and Democratic National Committee, including the emails of Hilary Clinton, together with the extensive information campaign conducted by the Russian troll factory – Internet Research Agency (Агентство интернет-исследований) – and related Russian media.
The actors participating in the Russian cyber activities include both state actors, with a significant role of the intelligence community, and non-state proxies. Aside from the GRU 74455 and 54777 Units, from Montenegro’s perspective, the 26165 Unit is the most relevant, which is behind the activities of the APT28 group (Advanced Persistent Threat 28) also known as Fancy Bear. Both the investigation of the U.S. Special Counsel Robert Mueller on the possible coordination between Russia and the presidential campaign of Donald Trump and the EU officials identified APT28 as a GRU 26165 Unit. APT28 uses sophisticated tools around the world, targeting Kremlin opponents. Even though the security companies such as ESET and FireEye have been identifying the activities of this group since 2004, these attacks have become more intense since 2014.
So far, the Russian activities in Ukraine have been the most complex and the clearest example of the Russian means and methods. Since Euromaidan in 2013 and the Crimea annexation the year after, Ukraine has been the testing ground for many Russian cyber capabilities. Ukraine has also fallen victim to distracting cyber-attacks on its electric energy infrastructure, which caused a power outage for a great part of the population in 2015 and 2016. Another attack on Ukrainian infrastructure occurred in June 2017 when the Ukrainian financial system was broken into; the data from the computers of banks, energy companies, high officials, and airports were deleted

Georgia is one of the first examples where the military and cyber operations and attacks were simultaneously used when it lost almost 1/5 of its territory in the 2008 war. The newer example is a massive cyber-attack on Georgia in October 2019, which illustrates the sophistication of Russia’s approach. The attack damaged servers in offices of the Georgian President, judicial system, municipalities, government, and non-government organizations, blocked sites, and disrupted TV stations’ broadcasting. In the Western Balkans, Russian cyber operations were used as an integral part of greater campaigns to obstruct the NATO enlargement process.
It was revealed that the APT28 was also responsible for attacks on German Bundestag in 2015, French television TV5 Monde, attempted attack on the Organisation for the Prohibition of Chemical Weapons (OPCW), Winter Olympic Games in Pyongyang in 2018, and Romania in 2017, as well as for numerous operations in Montenegro since 2016.
Russian Cyber-operations in Montenegro
Along with Northern Macedonia , Montenegro is the most significant target of cyber-attacks and espionage with Russian signature. These activities became particularly prominent during 2016 and 2017.
In the period of NATO accession finalization, which coincided with the parliamentary election in October 2016, Russia became significantly active and intensified its presence through disinformation campaigns of the Russian media, embargo on Plantaze wine and other products, coup attempt, and the GRU cyber-attacks, i.e., their APT28 group.
On the parliamentary Election Day in October 2016, Montenegro faced frequent DDoS attacks that targeted the sites of public institutions, pro-NATO and pro-EU parties’ web pages, pages of civil society, and election observers. Due to these efforts, the sites of news portals CdM, Antena M, and the Democratic Party of Socialists, inter alia, were taken down. The site of the Center for Democratic Transition (CDT), which monitored the election, could have not been accessed as well.
Besides DDoS attacks, the citizens were spammed by numerous anti-Government messages on the same day. They were coming from unknown numbers via Viber, Facebook, and WhatsApp. The Agency for Electronic Communications and Postal Services of Montenegro ordered a ban on these applications and similar communication services, which has been addressed to all telecommunication operators in Montenegro during that day. The operators were obliged to implement the measure in accordance with the Law on Electronic Communications, which stipulates that communication for the purpose of direct marketing is not allowed unless the user previously agreed to it. The act of blocking these platforms for several hours was condemned by the public, numerous local and international organizations, including the Reporters Without Borders
Facebook stated that this company was familiar with the disruption that affected the access to it in Montenegro, which occurred in October 2016 during the election. Four days after the election, on October 20, 2016, another phishing attack on the Parliament of Montenegro occurred; the group Fancy Bear probably was behind it again.
More intensive DDoS attacks (than those on the elections) occurred in January, February, and June 2017, disrupting the web services of the Government and state institutions, as well as some pro-Government media. Montenegrin Ministry of Defence also reported that they were the target of phishing attacks through e-mails that seemed to have been sent from the EU and NATO with attachments and provide hackers with an opportunity to install the malware Gamefish to the computers of the Ministry of Defence, which is a method that the APT28 uses. Gamefish is a Trojan that offers to a hacker good access to the targeted computer, including the exfiltration of data, access to the logs, and other surveillance options.
The Government stated back then that the scope and diversity of attacks, but also the fact that they were performed at the professional level, pointed out synchronized action. Three cyber security companies – FireEye, Trend Micro, and ESET concluded that the attacks came from APT28. The U.S. intelligence data additionally indicate that the group had connections with the Russian military intelligence service GRU and was financed by the Kremlin. After many attacks at the beginning of 2017, Montenegro sought help from NATO and the U.K., which helped to successfully stop two attacks at the end of the same year.
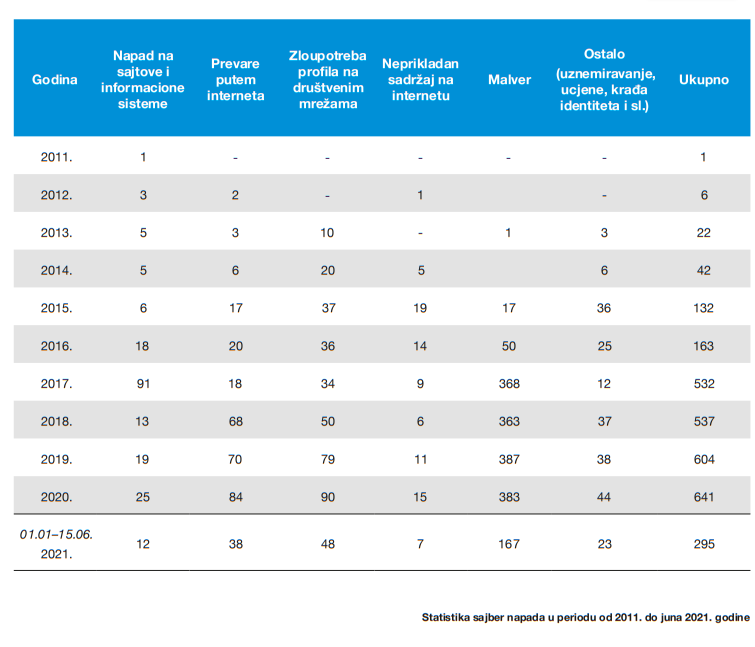
Analysis of the cyber threats to Montenegro published by the Ministry of Public Administration and presented in the Cyber Security Strategy of Montenegro 2018 – 2021, pointed out that the number of cyber-attacks rose in 2017, or, that it coincided with the final phase of Montenegro’s accession to NATO, which certainly does not imply that all of them were from Russia. During the first nine months of 2017, there were 385 reported incidents out of which 335 concerned malware and attacks on sites and state institutions. In comparison, there were only 22 attacks in 2013.
Since the attacks have become more frequent, Montenegro tightened defense measures and formed 31 local teams, in charge of cooperating with the members of the national Computer Incident Response Team (CIRT), concerning the protection from computer security incidents online.
CIRT said for the DFC that the number of attacks rose in comparison to 2017 but they are becoming more and more sophisticated, therefore, it is very difficult to trace perpetrators. CIRT worked on the investigation of DDoS attacks that occurred in 2016 and 2017, however, it could not determine for sure the accountability of any hacker group (contrary to the mentioned cyber security companies), during, and shortly after the attacks, since they were very complex, unlike the regular DDoS attacks.
Due to the previous events, at the beginning of October 2019, members of the U.S. Cyber Command arrived in Podgorica at the invitation of the Government of Montenegro in order to investigate the signs of Russian penetrating the networks of the Montenegrin government, but also to have an insight into the adversary cyber threats before the then-upcoming 2020 U.S. and Montenegrin election.
GRU Online Operations in Montenegro
Online operations are focused on the creation of fake media websites, bot accounts, and distribution of propaganda content harmonized with the official state narrative and goals, and they represent a par excellence example of the Russian modus operandi.
Among the data that Facebook submitted to the U.S. Senate Select Committee on Intelligence (SSCI) in 2019, there are clear and precise indicators and proofs of the ways that GRU and their APT28 used between 2014 and 2019 in order to create think tanks, alternative media, and avatar accounts on various social media in many countries, including Montenegro. This demonstrated that Russia had had an active role in the 2016 Montenegrin election and its attempted sabotage.
Modus operandi was simple – anti-NATO and anti-Western content from the GRU-created alternative media was supposed to be spread as much as possible, using fake Facebook, Twitter, and even Medium accounts, using adequate hashtags related to the Montenegrin elections and NATO accession, such as #NeUNato, #STOPMILO, etc.
Crna Gora News Agency
Out of 33 Facebook pages (all of them were deleted in 2018 in accordance with the Facebook inauthentic behavior policy) that were delivered to the U.S. Board, one of the fake media Crna Gora News Agency particularly stands out. CGNA’s Facebook page contained 1,530 posts. The page shared the content in Montenegrin (around 90% of the posts) and English (around 10%) with three related sites – cgna.info (does not exist), crnagoranevs.vordpress.com (does not exist), and cgna.me (in the moment of writing – porn site). The articles usually aimed at discrediting President Milo Djukanovic and NATO, and represented another step forward in the Russian aggressive media campaign.

Russian and pro-Russian Bulgarian media frequently republished the articles from CGNA, such as fake news on the European Commission’s fears that the electoral fraud would occur in Montenegro in 2016, which was another attempt of discrediting.

Besides mentioned topics, this fake Russian medium and Facebook page shared stories about Syria and supported Assad in its reporting (which coincides with the Russian official attitudes), followed by the anti-Hillary articles and numerous conspiracy theories.
The archived version of the CGNA website reads that Crna Gora News Agency is the first syndicated multimedia news service and strives to be the source of reliable and credible news on government, politics, economy, markets, business, sports, and lifestyle. The unclear and linguistically disputable structure of the sentences implies that the persons editing the content of the portal were not native speakers.
Avatar accounts
Besides pages, fake accounts of non-existing persons were created in order to make additional content and distribute the existing one on social media.
All fake accounts had particular similarities – they all claimed to be either independent and free journalists or students of postgraduate studies and published articles in the right-wing blogs/media that do not exist today such as Inside Syria Media Center (ISMC), The Informer, and Crna Gora News Agency. Likewise, many of them only published on one topic and had only one photo taken from the Russian VKontakte social media.
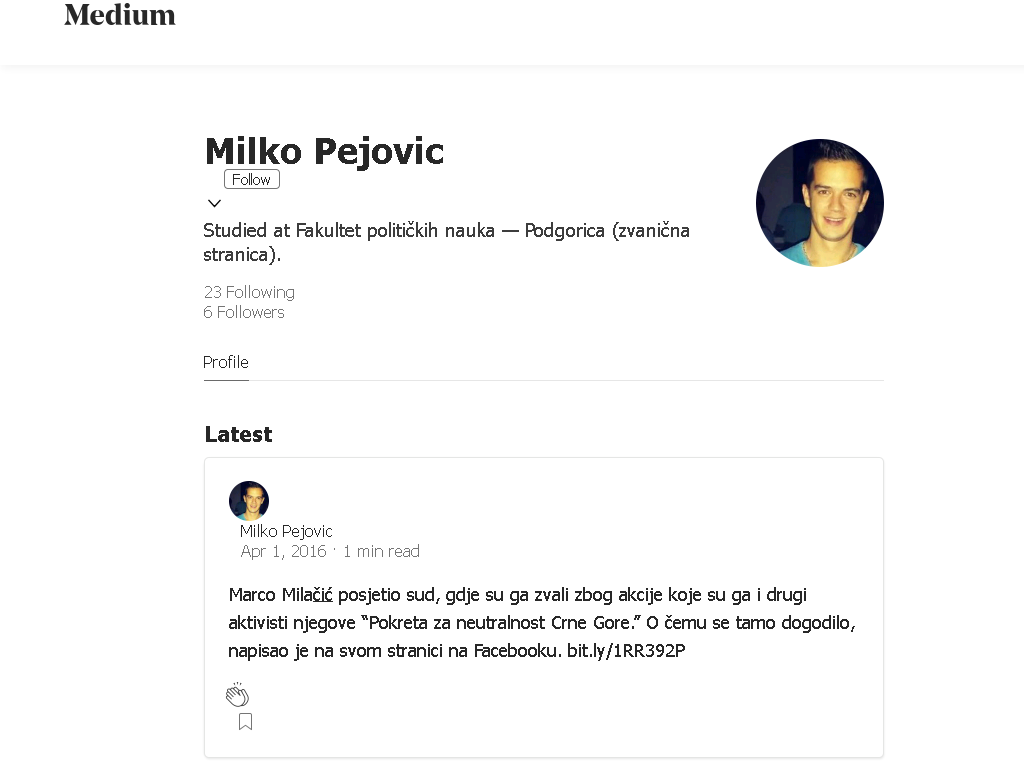
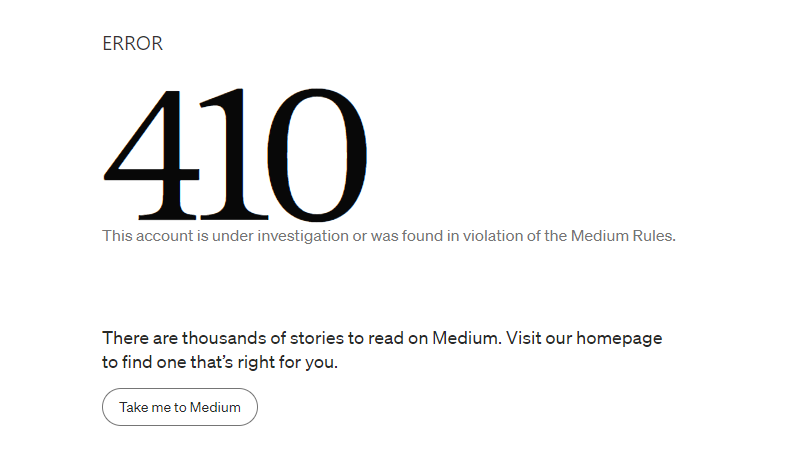
One of the important accounts in the context of Montenegro is Milko Pejovic, which was one of the few that shared the CGNA content, and one of five that followed the CGNA Medium page. On his Medium page, it is stated that he allegedly studied at the Faculty of Political Science in Podgorica. He published the articles about Montenegro on the pro-Russian site Globalresearch.
Jelena Rakocevic is also one of the few who published the CGNA posts and wrote articles for the alternative media that do not exist today, while she used the stolen photo of a real person from the VK network. In September and October 2016, she was very active on the site Forum-CG with the Russian domain (http://www.forum-cg.ru/=) where she only shared the CGNA content with hashtags #STOPMILO, #NEURAT, and #STOPNATO, and afterward, she completely stopped posting.

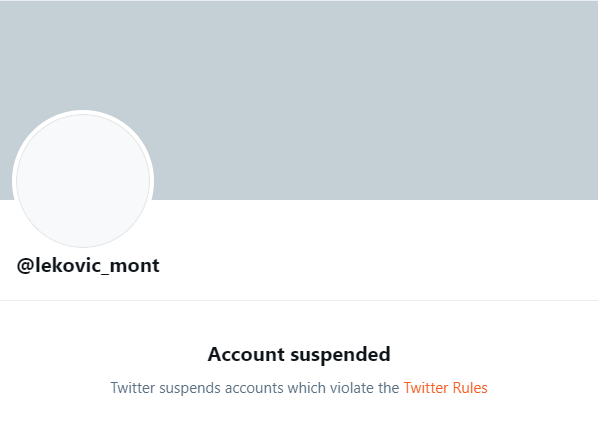
Also, there were Twitter accounts promoting the CGNA and anti-NATO content, created in 2016, and two of them, @lekovic_mont and @MilkoPejovic, stood out.
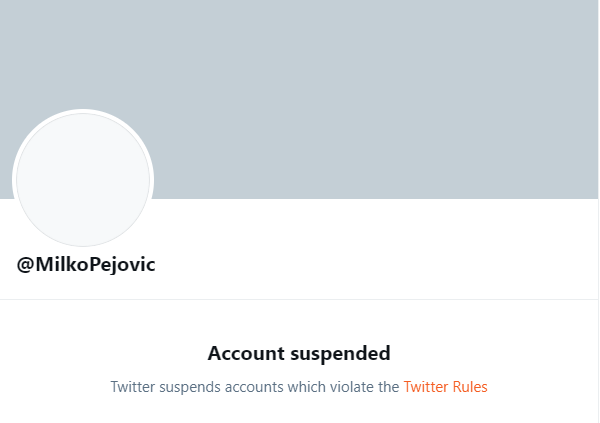
Milko Pejovic shared links for votemontenegro.eu platform created by Marko Milacic’s Movement for Neutrality where the citizens were able to vote online, using their Facebook profiles. In this case, it is indicative that the News Front, an FSB medium, shared posts and information on the referendum, presenting Marko Milacic as a courageous and brave guy whom the voters trust.

The other account frequently posted #NEUNATO, #ANTINATO, and #STOPMILO posts. After Facebook had recognized inauthentic behavior on their accounts on the platform, the accounts were deleted, and Twitter soon did the same.


Crna Gora News Agency and a joined network of fake accounts offer another view on the way that Russia updates and uses its influence mechanisms in the digital era. These data reveal the GRU’s attempts to insert Russian narratives in the Montenegrin media environment, even though their reach was very limited.
Established Russian Media at the Disposal of the Services
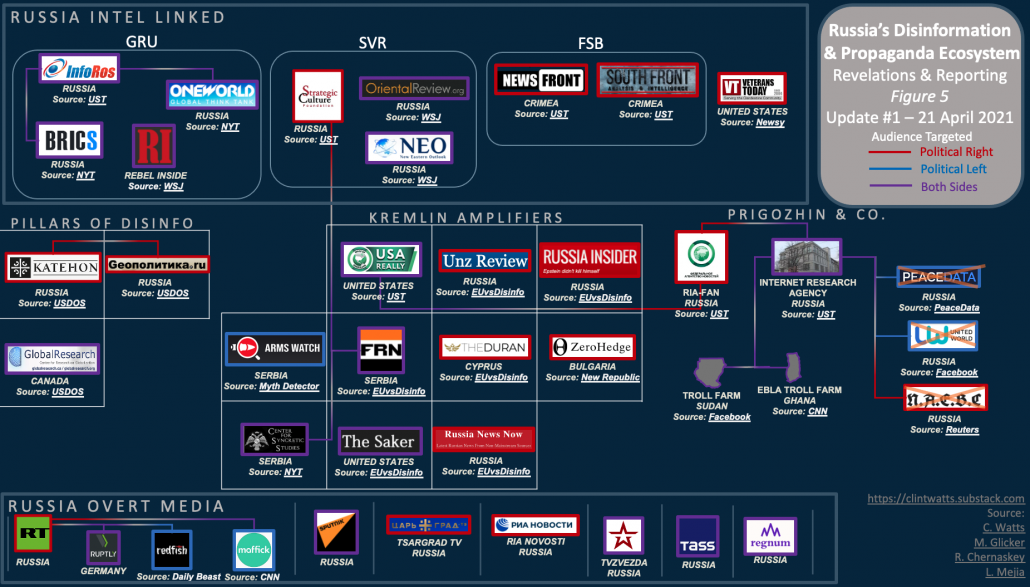
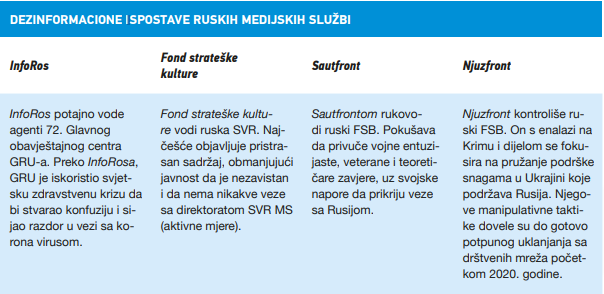
One of the channels used for spreading the Russian influence is the media that operate together with the services. Russian security services actively operate through the media, and they are no strangers to the creation of media outlets in order to spread the Russian narratives. The FSB, the GRU, and the SVR all manage the media network that made it to Montenegro as well.
LifeNews and FSB
LifeNews is a pro-Kremlin media organization launched in 2009, which has strong connections with the Federal Security Service. It is used for all purposes, such as the mudslinging of Kremlin opponents and planting disinformation. This media is headed by Aram Gabrelyanov, described by Lenta.ru as a man who abruptly succeeded from the provincial tabloid editor to one of the most influential Russian media moguls. Throughout 2011, Gabrelyanov was also the Chairman of the Board of Directors of Izvestia. He publicly calls the Russian President the father of the nation, and Putin recognized his contribution to Russian propaganda in Ukraine in May 2014 and awarded him the Order of Honor for objectivity and professionalism in covering events in the Republic of Crimea.
In the context of Montenegro, this medium is interesting since the leader of the True Montenegro Marko Milacic appeared on LifeNews television on May 21, 2016, on the occasion of celebrating the Independence Day of Montenegro, who strongly criticized the then Montenegrin government. Equally, LifeNews published articles on the Democratic Front campaign against Montenegrin accession to NATO and their reaction to the coup attempt and addresses to Sergei Lavrov.
Katehon and Geopolitica.ru
Katehon, a think tank organization and news portal with headquarters in Moscow, is in charge of spreading anti-Western disinformation and propaganda, and it is led by individuals associated with the Russian intelligence services. Board of Directors comprises Sergey Glazyev, former economic advisor to President Vladimir Putin; Andrey Klimov, Deputy Chair of the Federation Council Committee on Foreign Affairs; Leonid Reshetnikov, retired Lieutenant-General of the Russian Foreign Intelligence Service; and Alexander Makarov, retired Lieutenant-General of the Russian Federal Security Service.
During 2015, Katehon published numerous articles and tried to conduct a campaign against Montenegro’s NATO accession. The analysis showed a link between pro-Russian news portal IN4S and Katehon. The IN4S republished many articles from Katehon, usually targeting NATO, which was characterized as a private club of war criminals, and during 2016, the IN4S republished Katehon’s weekly geopolitical forecasts twice.
Also, in October 2016, Katehon republished the interview with general Leonid Ivashov, which Igor Damjanovic carried out in Moscow for the IN4S news portal. Katehon thanked Damjanovic and the IN4S news portal for the provided material. The interview was republished by the news portal Geopolitica.ru, also recognized as a platform for spreading disinformation, propaganda, and ideas of an ultranationalist Russian philosopher Alexander Dugin.
However, the interview with Ivashov was not the only Damjanovic’s contribution to Katehon and Geopolitica.ru. These news portals also contain his articles stating that the media in Montenegro were mudslinging Russia, that Montenegrins would not allow accession to the anti-Russian Alliance, and that the party of Milo Djukanovic was rigging the elections. Katehon, IN4S, and Geopolitica.ru were labeled in the U.S. Department of State’s Report as a part of a so-called propaganda ecosystem of the Russian disinformation campaign.
SouthFront
In the context of Russian media that are close to the security sector and launch disinformation, it is important to mention the news portal Southfront, focused on military and security issues. SouthFront is a site for spreading disinformation, registered in Russia, undertaking the FSB’s tasks. SouthFront tries to influence the military enthusiasts, veterans. and conspiracy theorists while it also tries to hide its links to the Russian intelligence service. Even though they try to hide their Russian roots in all possible ways, the news portal is registered in Moscow and their PayPal address has a Russian domain. Also, the owner or founder of this media is not known in public, but officer Viktor Stoilov, a Bulgarian marketing expert that manages a marketing company in Sofia, is mentioned as a part of its managing committee.
However, besides SouthFront, the name of Stoilov can also be found on Katehon and Geopolitica.ru, the news portals that he also writes his analyses for. It is also indicative that the pro-Russian news portal IN4S was also listed as a part of the SouthFront media network, which was removed from the SouthFront website in the period between October 31 and November 6, 2018. However, what was not removed from the website were the articles republished from IN4S.
InfoRos
Along with the abovementioned news portals, the connection was found between the IN4S and the news portal InfoRos, which is allegedly initiated by the GRU’s Main Intelligence Information Center (GRITs), also known as the 54777 Unit. GRITs is a Unit within the Russian Information Operations Troops, identified as Russia’s military force for conducting cyber espionage, influencing, and carrying out offensive cyber operations.
In 2018, the Washington Post labeled InfoRos and the Institute of the Russian Diaspora as the most significant organizations acting within the 54777 Unit, which was described as the center of the Russian military’s psychological-warfare capability. InfoRos used the network of websites, including declaratively independent web locations for spreading false narratives on conspiracies and disinformation promoted by the GRU officials.
In July 2020, the U.S. officials identified InfoRos as a platform that, along with managing the websites InfoRos.ru, Infobrics.org, and OneWorld.press, spreads disinformation on the COVID-19 pandemic. Denis Valeryevich Tyurin and Aleksandr Gennadyevich Starunskiy were identified as high-level members of InfoRos, who used to work for the GRU. And, according to the U.S. officials’ statements, they still maintain close ties with the GRU Unit where they worked as specialized military-psychological intelligence officers.
In its report from June 2020, the EU DisinfoLab analyzed connections between InfoRos, One World, and Observateur Continental on one side and the Russian intelligence service – GRU on the other side. The report says that the InfoRos is evolving in a shady grey zone, where regular information activities are mixed with more controversial actions that could be quite possibly linked to the Russian state’s information operations.
The EU DisinfoLab presented the secret connections between InfoRos and web page Observateur Continental that spreads disinformation and pro-Russian narratives in France, but also with One World, which reported on the 2020 parliamentary election in Montenegro. InfoRos is the news portal that republished a piece of news from the IN4S, referring to the number of people that attended the processions during 2020, and back in 2015, they published an article by Igor Damjanovic titled Fear of uncontrolled people’s uprising – Montenegro’s accession to NATO puts an end to economic development.
Strategic Culture Foundation
Strategic Culture Foundation is a medium and a think tank registered in Russia in 2005 and according to the State Department’s Report, Pillars of Russia’s Disinformation and Propaganda Ecosystem, it is under the authority of the Russian Foreign Intelligence Service and maintains close ties with the Ministry of Foreign Affairs of the Russian Federation. The basic tactic of this medium is to publish the statements of the Western intellectuals and conspiracy theorists, thus trying to hide its Russian origin, but also to reach the Western target audience. The General Director of the Strategic Culture Foundation is Vladimir Makimenko, who used to be the Director of the Russian Unity Foundation, whose goal was to promote a positive image of Russia and Russian culture abroad, especially among the so-called Russian compatriots. President of the Foundation is Yuri Prokofiev who was the Moscow Communist Party chief from 1989 to 1991 and a member of the Soviet Politburo but also one of the founders of the Russian Organization for Assistance to Special Services and Law Enforcement Authorities (ROSSPO). ROSSPO closely cooperates with the Russian security services in order to offer support to the Russian policies, facilitate the cooperation between state institutions and the civil sector, and provide social protection of the employees in intelligence services and law enforcement bodies. English version of the media focuses on world politics and security issues but it says nowhere that the news portal is registered and managed from Russia. It is evident that they are attempting to hide Russian origin and connection with the security services, but the Russian narratives on topics of Russian interest give them away. Here are a couple of examples The Skripal Case is a NATO False Flag Operation, The European Union was created by Nazis, Russians have Excellent Weapons, and similar.
It is indicative that this media in Russian reports on significant social and political events in Montenegro, such as NATO accession, processions, and elections. Based on the successful recipe, the following narratives are frequently pushed: after NATO accession, Montenegro is facing its end, the Law on Freedom of Religion or Beliefs from 2020 was an anti-church law, the Church in Montenegro is being persecuted, atheist Milo Djukanovic is creating his own church on the basis of Ukrainian scenario, Montenegro is trying to get rid of the criminal regime, mafia as a guarantor of the Euro-Atlantic integration. In 2019, this news portal republished the news that True Montenegro leader Marko Milacic set the NATO flag on fire as a protest against colonial politics of the Alliance. Strategic Culture Foundation had its subsidiary in Serbia but seven years after the website had been created, it stopped working in December 2017. The news portal IN4S extensively republished the articles of the Strategic Culture Foundation glorifying Russia and emphasizing the significance of Russia-Serbia relations while presenting NATO as an instability factor in the Balkans, that plans to put the whole Balkans in its pocket and then attack Russia. In 2015, the Strategic Culture Foundation carried out an interview with the then Bishop of Budimlja and Niksic Joanikije, and the topic was the situation in Montenegro. A former associate at the Ministry of Education, Science, Culture and Sports and then editor of the news portal Princip Vladimir Vukovic, previously mentioned in the analysis, was one of the speakers at the conference Balance of the Western Import of Democracy to the Territory of SFRY from 1990 until Today, organized by the Strategic Culture Fund in 2016. On that occasion, he emphasized that Montenegro was the best example of a country on the ex-Yugoslavia territory that was made upon the pattern of the Western democracy, that the citizens of Montenegro living in the totalitarian democracy were still waiting for the promised fruits of independence, while the tradition was being ruthlessly trampled upon, and historical relations with Russia were being deleted.

